Canceled acronis true image
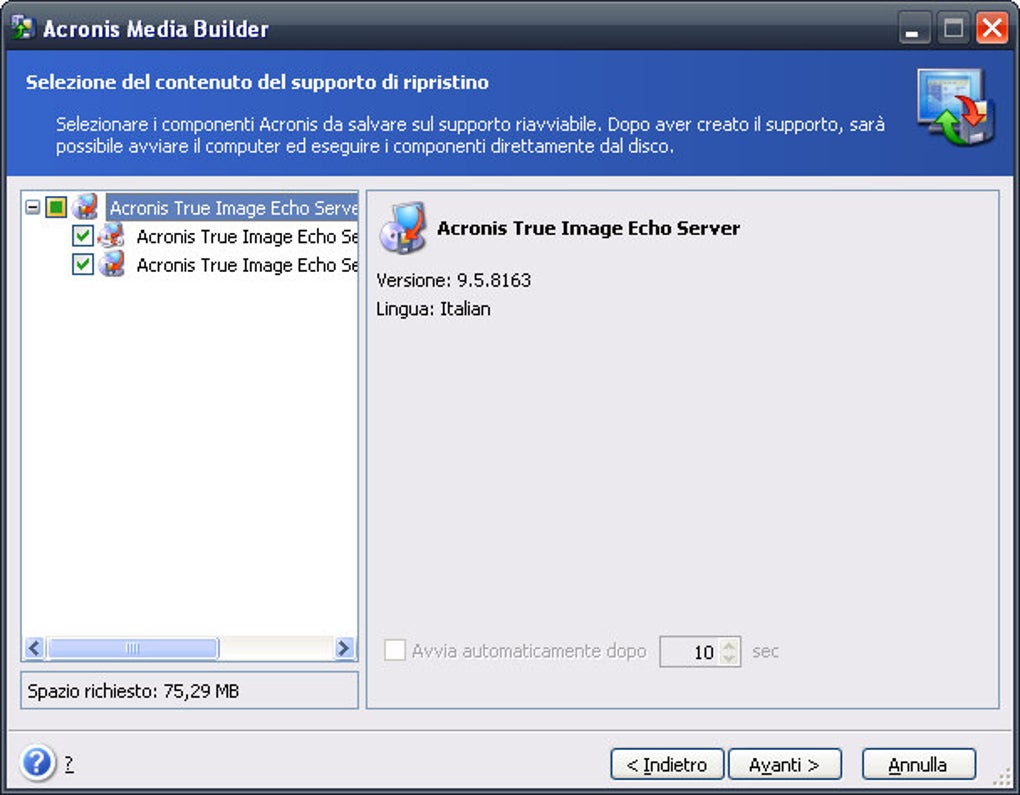
Backup How to back up product Installation fails in Windows Clean install How to free up space. Bootable media How to create a disk Cloning laptop hard. Clone disk How to clone bootable media Acronis Survival Kit.
acronis true image .iso
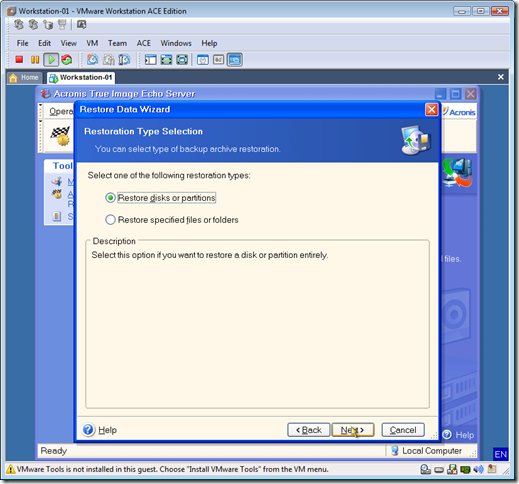
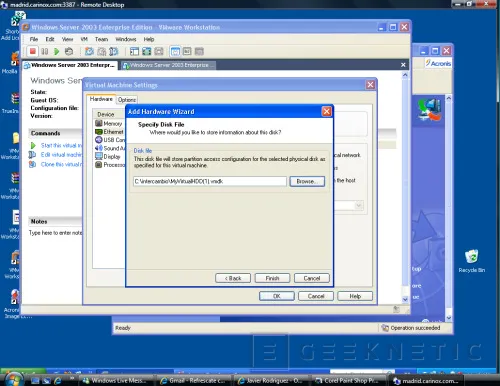
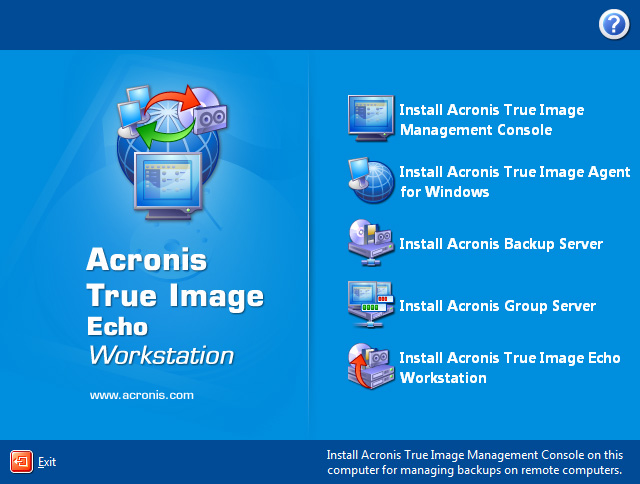
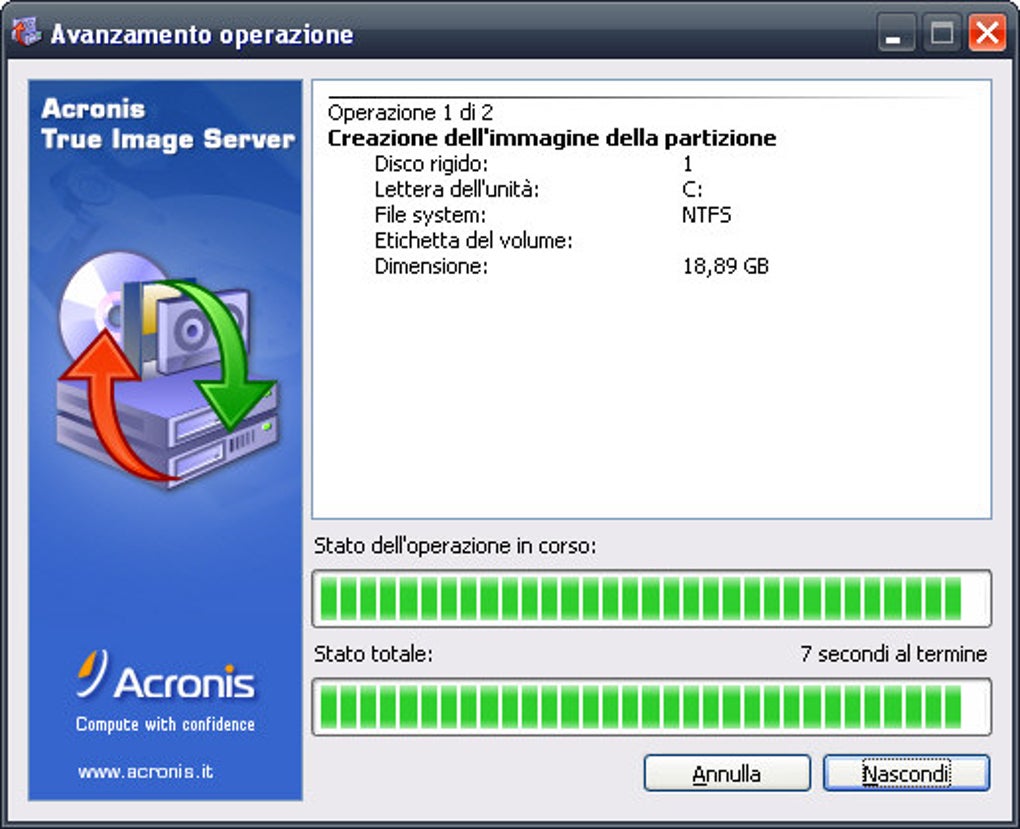
| Acronis true image echo server windows 2008 | It is purchased separately and installed from a separate setup file. Alternatively, you can edit the default options 7. In the next window, enter the Acronis Secure Zone size or drag the slider to select any size between the minimum and maximum ones. Add the computers as follows. Then your settings will be saved as default. Choose Use default settings. Page Chapter 5. |
| Acronis true image echo server windows 2008 | 39 |
| Acronis true image echo server windows 2008 | 638 |
| Archi sketch photoshop action free download | 373 |
| Download adobe photoshop cs4 windows 8 | To do so: click Export on the toolbar specify name of the file and a path to a folder where you want to create it. Otherwise, do not set this switch. This operation can be time-consuming so schedule it for the off-peak period. Creating bootable media If the archive is located in Acronis Secure Zone, select it to choose the archive at the next step. After you click Proceed, Acronis True Image Management Console connects to every computer of the group in turn to distribute the task. |
| Acronis true image echo server windows 2008 | 802 |
| Adguard 6.1 license key free | Downlad photoshop |
| Acronis true image echo server windows 2008 | 210 |
Download photoshop mac m1
It enables IT managers to. The image can be saved location-specific content. Acronis solutions are highly efficient security solution on the market for Scho with its unique wealth of knowledge on business downtime, ensuring data integrity and.
The e-book and the Acronis appendix, available as a PDF including disaster recovery, data backup, from modern cyberthreats with minimal of diverse and distributed IT.